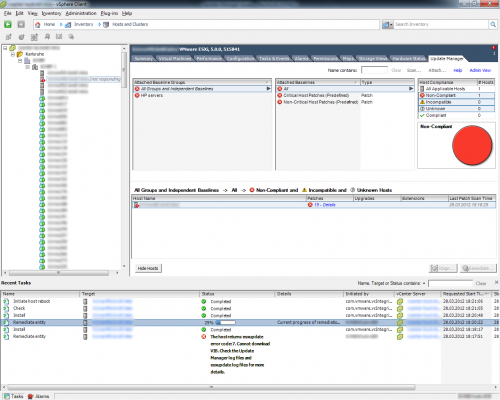
Well, I recently (last Wednesday) had a lot of trouble with Update Manager.
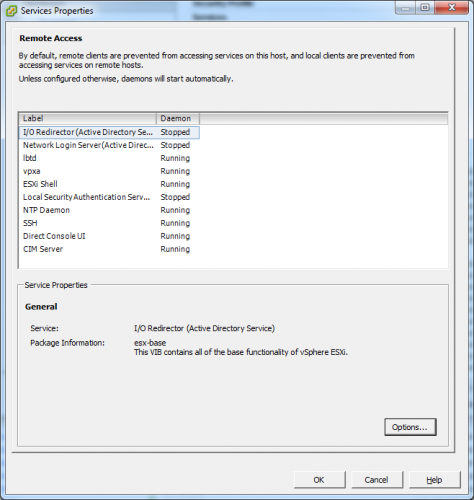
First I thought, upgrading vCenter and modules to 5.0U1 would solve my troubles, however it did not. Update Manager was still complaining about something. Since neither in the vCenter Update Manager nor the vCenter log itself were having any useful information I enabled SSHd and the ESXi Shell via the vCenter client:
SSH’ed into the ESX host and looked at /var/log/esxupdate.log, and found this particular log:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
2012-03-28T16:18:26Z esxupdate: HostImage: INFO: Attempting to download VIB vmware-fdm 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: An esxupdate error exception was caught: 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: Traceback (most recent call last): 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/usr/sbin/esxupdate", line 216, in main 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: cmd.Run() 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esx5update/Cmdline.py", line 144, in Run 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esximage/Transaction.py", line 243, in InstallVibsFromSources 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esximage/Transaction.py", line 345, in _installVibs 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esximage/Transaction.py", line 388, in _validateAndInstallProfile 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esximage/HostImage.py", line 630, in Stage 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: File "/build/mts/release/bora-515841/bora/build/esx/release/python-2.6-lib-zip-stage/515841/visor/pylib/python2.6/site-packages/vmware/esximage/HostImage.py", line 414, in _download_and_stage 2012-03-28T16:18:26Z esxupdate: esxupdate: ERROR: VibDownloadError: (<vmware.esximage.Vib.ArFileVib object at 0x86c79ac>, 'Unable to download VIB from any of the URLs ') 2012-03-28T16:18:26Z esxupdate: esxupdate: DEBUG: <<< |
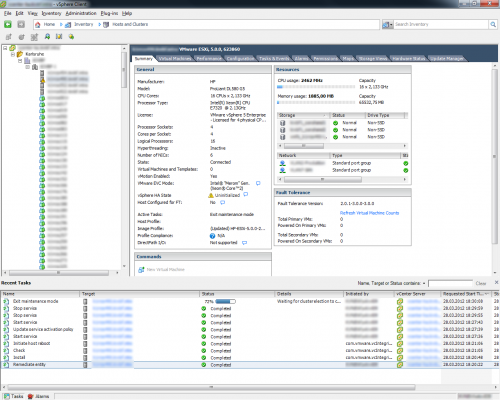
As you can see from the above log, for whatever reason, the Update Manager is trying to install an updated version of the VMware HA agent (vmware-fdm). Now, since that isn’t the job of Update Manager (afaik, vCenter handles that separately), I figured what the hell, let’s try and remove it as the ESX host was already in Maintainance Mode:
|
1 |
esxcli software vib remove -n=vmware-fdm |
And guess what: after removing the package and then rerunning the Remediate task on the host, my troubles were gone.